AI Ready: The Complete Guide to AI-Powered Cybersecurity Training in 2025/2026
June 10 2025
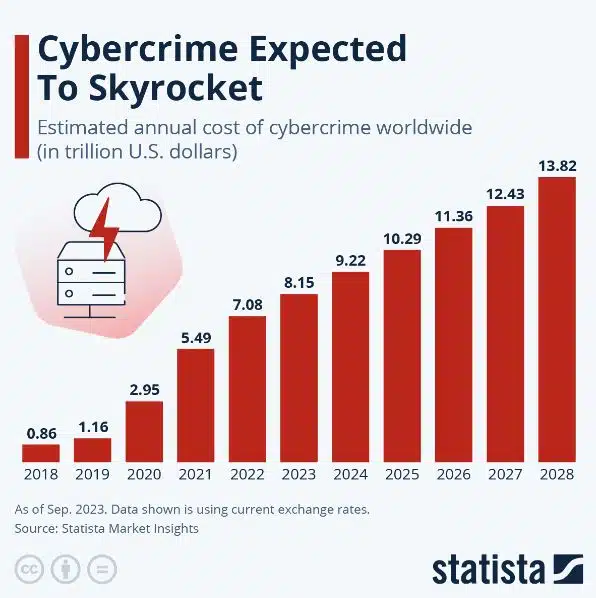
Introduction: The AI Cybersecurity Crisis The cybersecurity landscape has fundamentally changed. AI-powered cyberattacks are projected to surge by 50% in...