Voice Phishing, also known as ‘vishing’, is a growing form of attack, with 83% of organizations reporting it as a threat, and yet almost 75% of people don’t even recognize the term. Here’s what you need to know.
What is Voice Phishing (Vishing)?
Voice phishing attacks (also known as vishing attacks) are phone scams that start by voice, and then encourage users to go to a specific website and enter their usernames and passwords. In January 2021, the FBI has issued a warning about the increase in vishing attacks, and the use of VoIP technology to encourage employees to sign into a phishing website, where their usernames, passwords, and other sensitive credentials are stolen.
Today, these threats, and similar scams that start with voice communication, are becoming increasingly serious, especially as hackers take advantage of the global pandemic, and its associated fears and anxiety. What we can call ‘Coronavirus phishing’ leverages anything from masks and PPE, to vaccines and COVID-19 tests, and has become a mainstay of the threat landscape. These often prey on the most vulnerable, and businesses need to adapt to suit.
Without a doubt, and in line with the majority of advice from security professionals, security awareness training that offers personalized and relevant training content is a fundamental pillar in protecting against all kinds of phishing scams. While you can implement certain best practices operationally, such as Multi-factor Authentication, your employees are on the front-lines, and they need your support.
The Challenges of Training Against Voice Phishing Attacks
Security awareness training for an issue like voice phishing is easier said than done. There are three main reasons for this.
Risk Measurements Make the Threat Look Smaller Than it is: In large companies and enterprises, the percentage of vishing attacks in relation to phishing attacks as a whole is relatively minor. This type of attack may only be aimed at a single user and their credentials, but ignoring the risk is a short-sighted approach to take. Once a single user has been compromised, often without their knowledge, attackers have gained a foothold inside the network, and can make lateral movements through privilege escalation, for example.
Voice Phishing Simulations are Non-scalable: Voice phishing cannot be automated. Although this reduces the risk to the company, as it can only target a single user at a time, this also means that security awareness training is difficult to scale. Unlike traditional phishing simulations that can be sent widely across an organization, vishing is a new entity that needs its own type of training.
A Current Lack of Learning Methodology: Emails can be easily reproduced, and analyzed to isolate the threat pattern. Voice calls limit the ability to learn, as you can’t listen to the phone call over again and draw any conclusions or lessons. Training therefore needs to be aimed at understanding the threat of phishing more widely, and changing behavior around internet security as a whole.
A Positive Security Culture Encourages Employees to Be More Aware of Email AND Phone Scams
At CybeReady, we created our security awareness program with Koleb’s learning approach as our inspiration. The statistical model, as shown below, creates a four-stage learning cycle that has been proven to gently change employee behavior. This is especially relevant in an environment like security, where as we’ve said above, we are not always aware that we’ve even made a mistake.
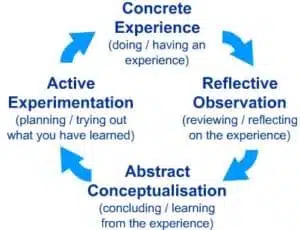
By actively triggering the reflect and learn sections of the cycle through phishing simulations, we allow employees to implement what they’ve learned the next time, which then rewrites the negative experience into a positive one.
For this to be impactful, we’ve found that this has to be a continuous offering (at least every month), and it has to reach 100% of employees. While it’s highly challenging to test 100% of employees with vishing scams, you can ensure that cybersecurity awareness training reaches the whole organization, so that you’re teaching employees how to generalize and spot attacks, through a practice makes perfect approach.
This technique also allows you to isolate high-risk employees, who are different from those that are simply beginners to a technical role, or less aware of the types of phishing scams that are common. While the latter category of employees may well experience a quick learning curve and become low-risk within a small number of simulations, high-risk employees will consistently fall victim to scams, and may need additional support. When isolated, this high-risk group can be targeted for more direct training, including educating them against more niche threats such as vishing, and phone scams.
Above All… Keep it Positive
Through years of growth, we’ve learned that bombarding employees with restrictions, warnings, and prohibitions doesn’t get your organization anywhere. Employees need a gentle guide through the ever-changing landscape of cyber threats, allowing them to learn in a low-pressure and non-threatening way that actually aids knowledge retention and learning.
Looking to equip your employees with the valuable tools and insight that they need to spot a phishing scam from any direction? Get in touch to schedule a demo.













