Today, we work in a global business environment where digital transformation is not a trend but a necessity. Software as a Service (SaaS) solutions have become the backbone of modern business operations. These cloud-based services offer unparalleled flexibility, scalability, and efficiency. However, with great power comes great responsibility, particularly in cybersecurity.
The rise in SaaS has also come with the increasing sophistication of its evil twin: cyber threats. The sheer volume of sensitive data handled by SaaS platforms makes them a hotbed for potential security breaches. Unfortunately, a recent SaaS industry survey discovered that 55% of organizations report experiencing a cybersecurity incident in the past two years, and 58% estimate that their current SaaS security solutions only cover 50% or less of their applications.
This critical shortfall in the face of ongoing threats makes robust SaaS security more essential than ever. Join us as we navigate the complexities of protecting your digital assets in the cloud, offering actionable insights and expert advice. Whether you’re a startup, a growing business, or an established enterprise, understanding the what, why, and how of SaaS cybersecurity is the first step toward safeguarding your digital future.
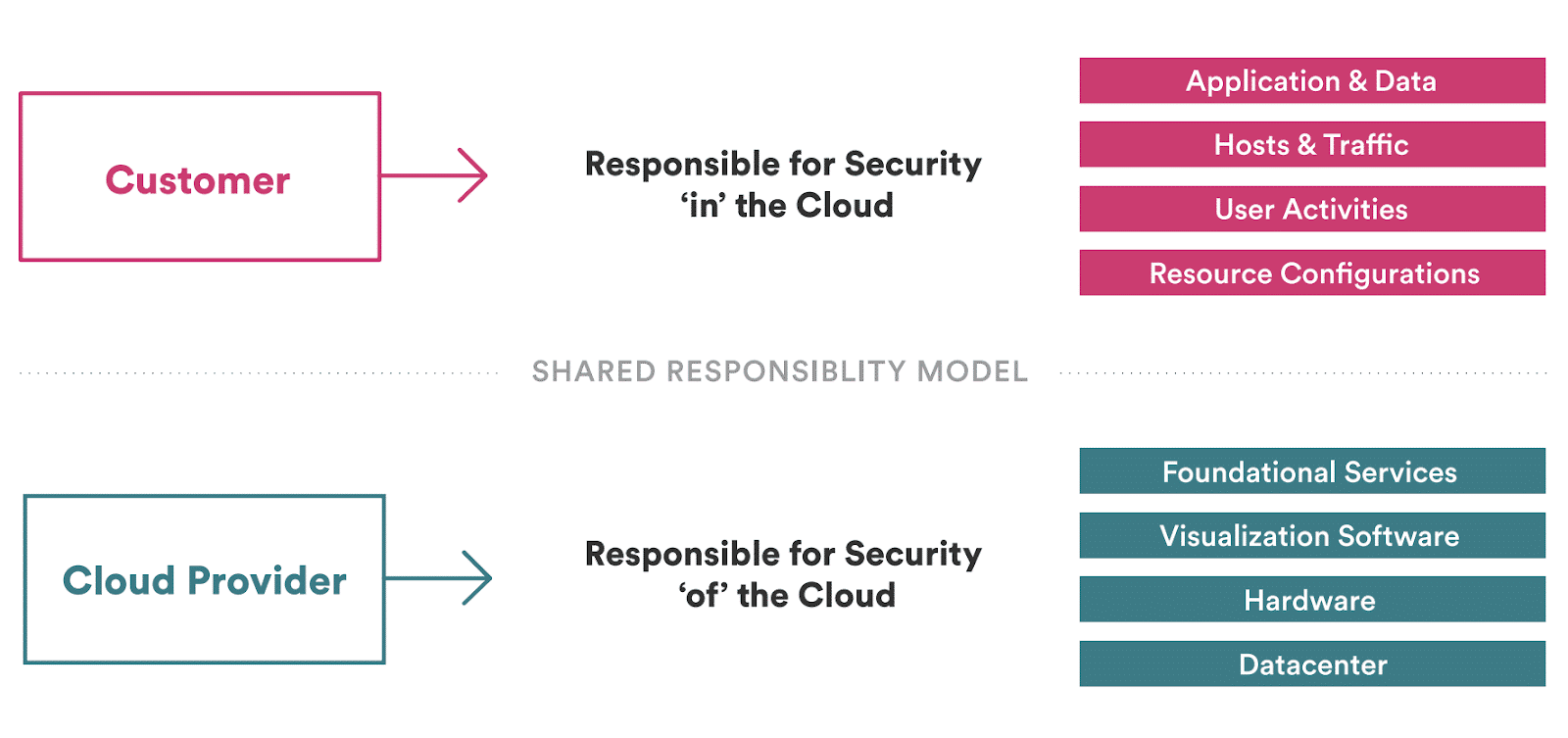
SaaS security is a set of measures an organization implements to safeguard data and accounts accessible via cloud-based third-party services. The service provider and the client share the responsibility for ensuring this security.
SaaS platforms are designed for remote access from various devices and locations, offering flexibility and speed. However, this also broadens the potential for cyber attacks.
The complexity of SaaS security is amplified by the fact that an average company may use over 130 different SaaS platforms, each with its own data access levels, server-side security by third-party providers, and varying user account security.
Integrating third-party services in SaaS solutions introduces additional security risks, often beyond direct control. Shared responsibility in SaaS security can lead to overlooked vulnerabilities and defense gaps. Maintaining regulatory compliance also becomes more complex with multiple SaaS vendors, especially across different legal and industry standards.

SaaS security can be understood through a six-level model, addressing both provider and client responsibilities:
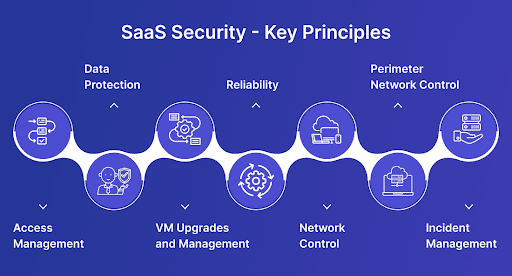
The seven principles of SaaS security are guidelines that help ensure the security and integrity of Software as a Service (SaaS) platforms:
Implement encryption, access controls, and regular backups to safeguard data from unauthorized access and leaks.
Utilize strong authentication, like multi-factor authentication, and manage user permissions effectively.
Deploy anti-malware, intrusion detection systems, and conduct continuous monitoring for timely threat identification and response.
Adhere to relevant data protection and privacy regulations like GDPR or HIPAA, based on geographical and industry-specific requirements.
Regularly conduct security testing (penetration tests, vulnerability assessments) and secure the application code.
Maintain secure infrastructure through secure architecture practices, regular audits, and established incident response plans.
Foster a security-conscious culture by educating users on security best practices and potential threats like phishing.
SaaS security is vital because it enables safe access to data and services for anyone in your organization, regardless of location. It plays a crucial role in warding off cyber attacks, safeguarding critical systems and data, and minimizing the chances of expensive incidents and downtime.
Data breaches can severely damage an organization’s reputation, lead to customer loss, and result in significant legal penalties. SaaS security maintains continuous business operations without interruption due to data loss or cyber attacks. An effective security strategy fortifies trust in your organization and ensures compliance with regulatory requirements.
Begin by mapping out your SaaS apps, identifying which teams use them, the data they access, and your security needs for each. This map should detail each app’s function, vendor location, third-party integrations, and relevant security controls.
Determine and assign security responsibilities for each app among stakeholders and users. This ensures no gaps in security due to unclear roles. Remember, security involves the vendor, your organization, its IT or cybersecurity departments, and individual users.
Implement a Zero Trust model, granting access based on specific user roles and tasks. Access rights should be strictly need-based, requiring user authentication for each action. This minimizes risks associated with compromised accounts.
Continuously monitor all SaaS applications and regularly liaise with vendors to understand the current security landscape, identify vulnerabilities, and enhance monitoring or access controls as needed.
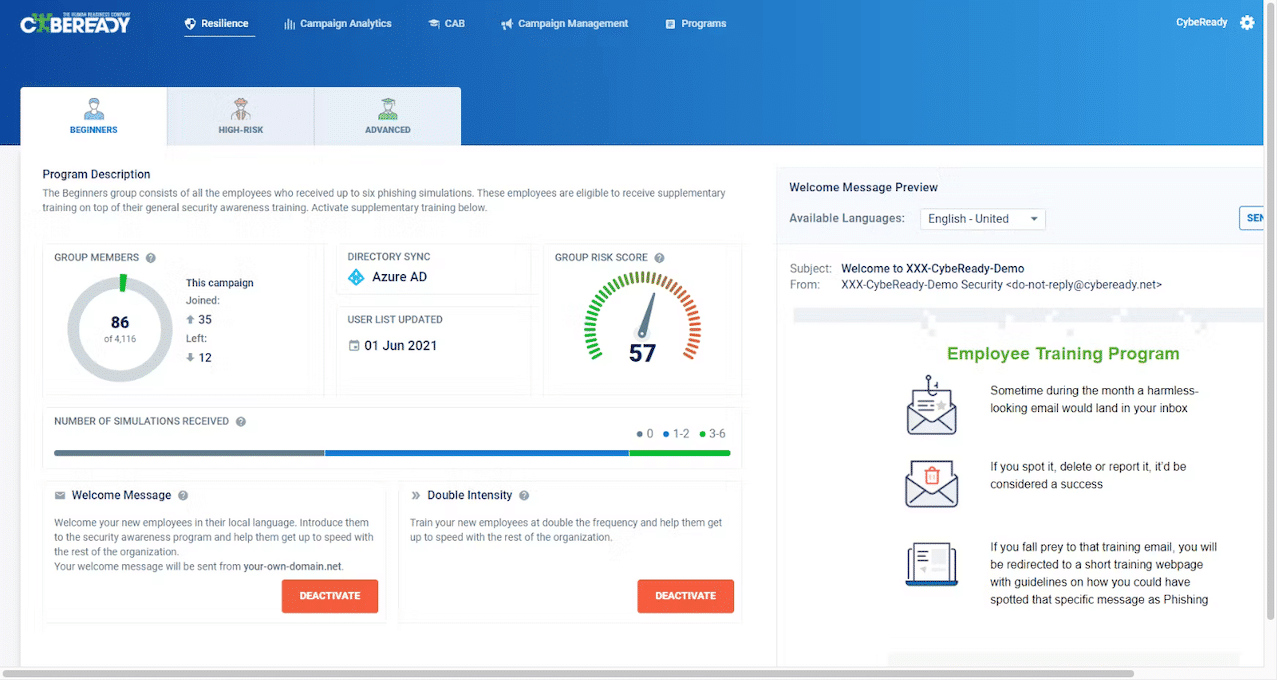
Educate employees on recognizing cyber threats like phishing, and adhering to cybersecurity best practices. Tools like CybeReady can offer engaging training to reinforce your team’s frontline defense against cyber threats.
Deploy AI and behavior analysis-based cybersecurity solutions for real-time threat detection. These can offer round-the-clock monitoring and alert you to potential attacks by analyzing network traffic and access patterns.
Prepare for potential breaches with a well-defined incident response plan. This plan should outline immediate actions post-breach, clearly assigning responsibilities to each involved party.
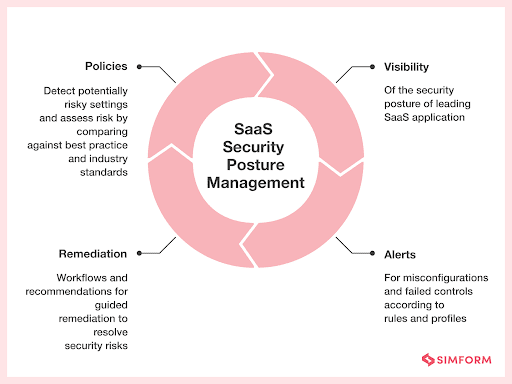
SaaS Security Posture Management (SSPM) is a security management methodology for SaaS. In SSPM, InfoSec teams use technology and automation to oversee the security status of their technology stack. The approach incorporates automated tools that provide extensive visibility into the organization’s infrastructure and the security of SaaS applications.
SSPM plays a crucial role in the early detection of cybersecurity threats, allowing for quick action and minimizing potential impacts. As businesses increasingly adopt SaaS applications for processes, user data, and CRM solutions, efficiency improves—but the attack surface also expands. SSPM counters this by keeping security teams informed about their tech stack’s security state, ensuring adherence to software security regulations.
In operation, SSPM tools perform continuous evaluations of SaaS applications across several critical areas:
SaaS Security Posture Management greatly simplifies the complex task of securing SaaS environments. Its benefits include:
SSPM offers a comprehensive solution for securing your SaaS portfolio. It provides insights into user interactions with SaaS applications, proactive threat alerts, and clear guidance on responding to data incidents, all within an automated, user-friendly platform.
With security breaches on the rise, SSPM plays a critical role in identifying and alerting security teams about both intentional and unintentional misconfigurations. It ensures robust access control and keeps a vigilant eye on deviations from standard security procedures.
SSPM eases the burden of adhering to complex internal and external security regulations, including industry-specific policies like HIPAA and CJIS. It automatically notifies administrators and security teams of any non-compliance, enabling swift action to uphold standards.
In the ever-evolving SaaS landscape, SSPM facilitates smooth transitions. It keeps security and IT teams updated about changes in the SaaS portfolio, streamlining platform migrations and ensuring all users adapt effectively.
SaaS Security Posture Management enhances your tech infrastructure’s security with these essential features:
SSPM consolidates essential information, from user data to threat intelligence, on a single dashboard. This user-friendly interface lets your team quickly manage risks and ensure business safety.
SSPM offers comprehensive visibility into your digital environment, promptly alerting security personnel to any suspicious activities, including policy misconfigurations.
With its enhanced monitoring capabilities, SSPM rapidly identifies and resolves issues, proactively mitigating threats to protect your organization.
Beyond threat management, SSPM also aligns your security practices with industry standards. It conducts activity evaluations and audits to spot vulnerabilities and verify compliance with security benchmarks.
SSPM can be tailored to fit your organization’s specific needs, working in tandem with your security team and auditors. This flexible approach ensures continual compliance and strengthens data security across various sectors.
SSPM is integral for bolstering your security infrastructure. Selecting a SaaS Security Posture Management solution that aligns well with your existing and future digital technologies is crucial. Opt for a system capable of handling at least 60 integrations, allowing it to evolve with your organization’s needs.
When integrating SSPM, assess its proficiency across various security domains, such as:
Ensure your SaaS Security Posture Management solution adheres to industry standards, with a strong emphasis on rapid threat detection and response. Key functionalities include real-time configuration change alerts, privileged user activity monitoring, and a comprehensive timeline view of your SaaS landscape for effective change tracking.
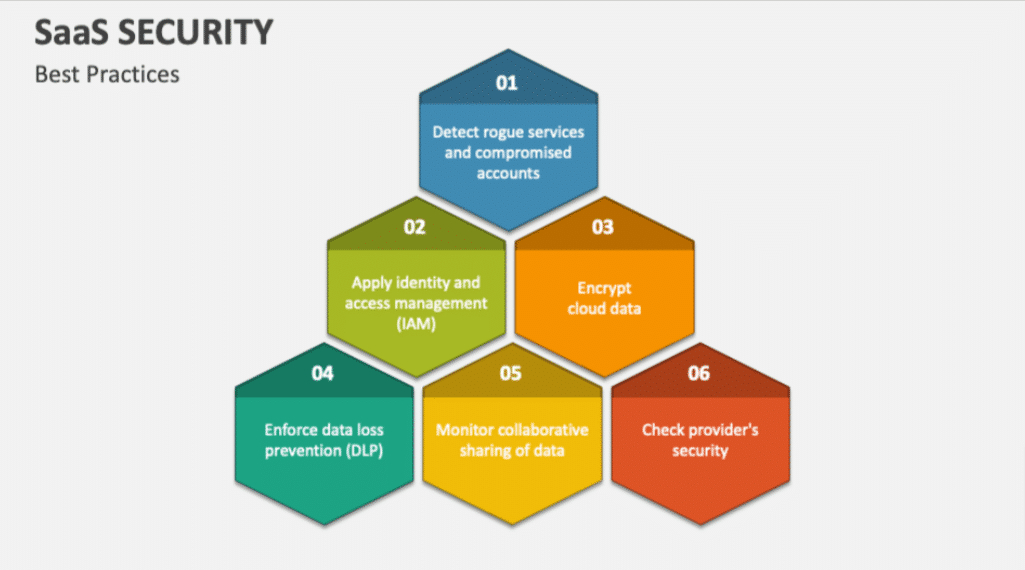
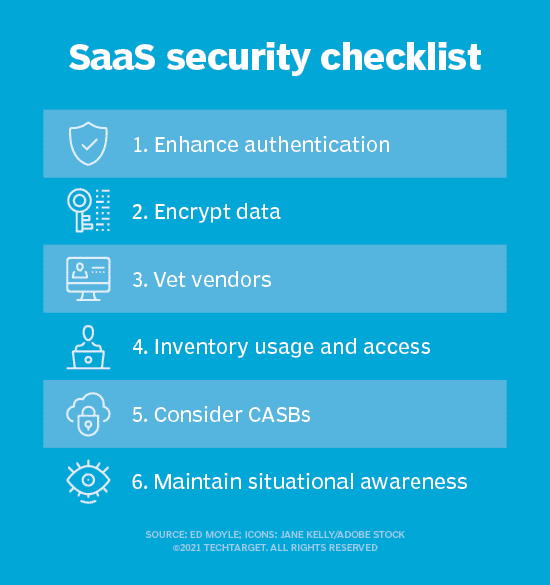
To enhance SaaS Security Posture Management and protect your digital infrastructure against evolving cyber threats, consider the following best practices:
Regularly backup customer data on various cloud platforms. This diversification is critical for disaster recovery and prevents complete infrastructure compromise in the event of a system failure.
Enforce strong password policies to deter hackers from using publicly available information to access your systems. This step is critical in preventing data breaches.
Gartner reports that up to 2024, 99% of cloud security failures will be from user actions. Educating customers on data safety during onboarding creates an additional security layer for your organization.
Encrypting all data, including internal communications and customer interactions, renders it indecipherable to cyber attackers, providing a solid defense layer.
Develop comprehensive security training for your employees. Utilize platforms like CybeReady within your cybersecurity strategy for programs that prepare your team against cyber threats.
SaaS security tools are specialized software designed to safeguard cloud applications and data accessible to anyone online. The attributes that render SaaS convenient for companies, such as quick account setup, remote access, and API integrations, also expose them to potential threats—so many of these tools identify and avert cyber attacks.
SaaS security tools are also essential for maintaining compliance with regulatory standards, offering assurance to clients and partners about protecting their data. Ultimately, SaaS security tools protect your organization’s business continuity, customers, and reputation.
SaaS’s extensive attack surface and numerous potential vulnerabilities necessitate a variety of security tools, including:
SaaS security tools should ideally have several of the following features to ensure comprehensive protection:
SaaS platforms, while highly beneficial, introduce significant security challenges that must be addressed by SaaS security. The implementation of SaaS Security Posture Management (SSPM) utilizes a combination of technology and automation to mitigate these challenges.
However, it’s essential to recognize that no technological solution is entirely foolproof.
To enhance the security benefits provided by SSPM, organizations must focus on the awareness and education of employees. This approach ensures a more comprehensive and effective defense against potential cyber threats.
This is where CybeReady becomes a critical component of a robust SaaS security strategy. Cybersecurity awareness training is indispensable in fortifying your organization against security breaches. Our training programs are designed to develop a company culture that prioritizes cybersecurity awareness, filling in the gaps where technology alone might not suffice.
Sign up for a demo today to discover how CybeReady redefines cybersecurity education and SaaS security.





Copyright © 2025 – CybeReady
We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit
Wir werden uns in Kürze bei Ihnen melden.
Schauen Sie sich bitte in der Zwischenzeit das kostenlose CybeReady CISO Tool Kit an.
We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit, or visit Our Blog
We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit, or visit Our Blog