In our digitally interconnected world, where cyber threats loom large and data breaches are rising, Data Loss Prevention (DLP) has transcended its status as a mere checkbox on an information security checklist. It has become an absolute necessity for organizations striving to protect their sensitive data from falling into the wrong hands.
The stark reality is that two out of three midsize businesses have already suffered the devastating blow of a ransomware attack in the past 18 months, as revealed by the latest 2022 MSP Threat Report by ConnectWise. And if that isn’t alarming enough, consider this: IBM estimates the global average cost of a data breach is a staggering $4.35 million, a financial burden that can permanently cripple an organization.
In this post, we will explore what data loss prevention is and why it is a critical factor in securing your organization’s data. We’ll cover the different types of DLP tools, the benefits and the essentials for building and implementing a strong DLP policy. You’ll discover the true power of DLP and unlock the secrets to safeguarding your organization’s most valuable asset: its data.
Data loss is a significant organizational concern for all industries. It refers to the unauthorized exposure, leakage, or destruction of sensitive data, which can have severe consequences such as economic loss, reputational damage, and legal ramifications. Data loss occurs for many reasons, including insider threats, external attacks, accidental actions, or system failures. To combat data loss effectively, organizations implement DLP strategies.
DLP involves a set of policies, processes, and technologies designed to identify, monitor, and protect sensitive data from unauthorized access, disclosure, or loss. The primary goal of DLP is to prevent data breaches, maintain regulatory compliance, and safeguard critical information assets.
DLP solutions detect, mitigate, and prevent data loss incidents. These solutions employ techniques such as content inspection, contextual analysis, and behavioral monitoring to identify sensitive data and enforce security policies. By implementing DLP, organizations can proactively identify and mitigate risks associated with data loss.
The importance of DLP cannot be overstated in a data-driven world. Organizations deal with vast amounts of sensitive information, including customer data, intellectual property, financial records, and confidential business data. This information becomes vulnerable to unauthorized access or accidental exposure without proper safeguards, leading to detrimental consequences.
Data breaches can have serious financial, legal, and reputational consequences for organizations. In addition to direct economic losses from data theft, organizations can face regulatory fines and legal fees and suffer damage to their reputation and customer trust. As the number of cyberattacks, hacks, and data breaches grows, it’s critical for organizations to implement robust DLP solutions to protect their sensitive data.
Moreover, compliance with data privacy regulations such as GDPR, CCPA, PCI and HIPAA is mandatory for organizations that handle sensitive data. Failure to adhere to these regulations can lead to penalties and legal consequences. By implementing DLP solutions, organizations ensure that their data-handling practices comply with these regulations.
Additionally, DLP solutions provide organizations with operational efficiency by automating data protection processes and identifying potential data security gaps. This enables organizations to optimize their data protection efforts and minimize the time and resources spent on manual data security measures.
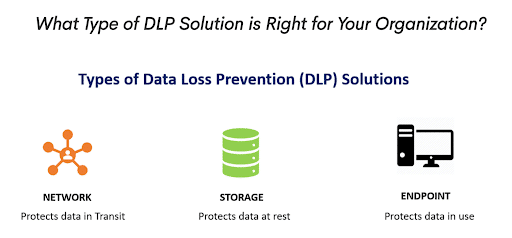
Different types of DLP solutions are available to address specific data loss risks and challenges. These include:
This type of DLP focuses on monitoring network traffic to identify and prevent the unauthorized transmission of sensitive data. It examines data packets for sensitive content and applies security controls to prevent data exfiltration.
Endpoint DLP solutions protect data on individual devices such as laptops, desktops, and mobile devices. They monitor and control data transfers, implement encryption measures, and detect and block unauthorized data transfers.
This DLP approach focuses on securing data stored in databases, file servers, and other repositories. It involves classifying and encrypting sensitive data, implementing access controls, and monitoring data access activities.
The increasing adoption of cloud services means organizations need DLP solutions to protect data stored and accessed in cloud environments. Cloud DLP ensures data security in cloud storage, collaboration tools, and cloud-based applications.
By understanding what DLP is, its importance, and the different types available, organizations can make informed decisions about implementing the most suitable DLP strategies and solutions for their specific needs. Protecting sensitive data is a significant priority for organizations to maintain trust, comply with regulations, and safeguard their business operations.
DLP tools are essential in today’s business environment, where data is constantly generated, processed, and shared across multiple channels. With the increasing sophistication of cyber-attacks, it is critical to have a proactive approach to data security. DLP tools provide organizations with a comprehensive view of their data landscape, helping them to identify and classify sensitive data.
The tools enable organizations to create policies and procedures for managing the data effectively and efficiently, reducing the risk of data breaches, and ensuring compliance with relevant regulations. DLP tools monitor data activity in real time, allowing organizations to identify and respond to threats quickly. They can identify attempts to access, copy, or transfer sensitive data and alert security teams to take action. DLP tools also provide insights into data usage patterns, enabling organizations to optimize their data protection efforts and improve operational efficiency.
With the rise of remote work, cloud computing, and mobile devices, DLP tools have become even more critical. They provide a centralized approach to data security, enabling organizations to manage data across multiple endpoints and platforms. This helps to prevent data loss, protect sensitive data, and ensure compliance with regulations, no matter where the data resides.
Various types of DLP tools are available, each catering to specific data protection needs. These include:
Content-aware DLP tools analyze data content, including text, images, and files, to identify sensitive information such as personally identifiable information (PII), financial data, or intellectual property. These tools employ advanced algorithms and machine learning techniques to classify and protect sensitive data accurately.
Endpoint DLP tools focus on securing data on devices like laptops, desktops, and mobile devices. They monitor data transfers, apply encryption measures, and enforce policies to prevent unauthorized data exfiltration or leakage from endpoints.
Network DLP tools monitor network traffic to detect and prevent unauthorized sensitive data transmission. They analyze data packets in real-time, apply predefined policies, and block or quarantine data that violates security rules. Network DLP tools are particularly useful in protecting data in transit.
With the rise of cloud services, organizations require DLP tools to protect data stored and shared in cloud environments. Cloud DLP tools offer functionalities such as data classification, encryption, access controls, and activity monitoring to safeguard sensitive information within cloud platforms.
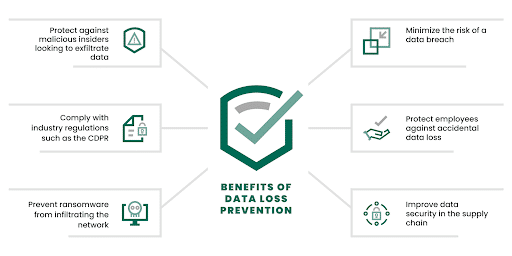
DLP tools offer many benefits to organizations, including the ability to:
Some essential features of DLP tools include:
By leveraging the capabilities of DLP tools, organizations can enhance their data protection measures, safeguard sensitive information, and maintain customer and stakeholder trust.
Learn more at: Top 9 Data Loss Prevention (DLP) Tools
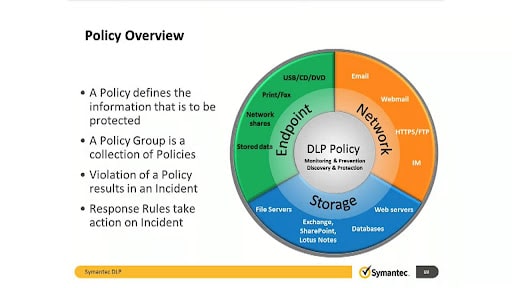
A Data Loss Prevention (DLP) Policy is a set of guidelines, procedures, and rules established by an organization to govern the protection and handling of sensitive data. It outlines the necessary measures, controls, and practices that employees must adhere to prevent data loss, leakage, or unauthorized access.
By defining guidelines, procedures, and rules, a DLP policy establishes a framework that sets expectations and standards for data protection. It identifies the types of data that are considered sensitive and specifies the appropriate handling and storage practices for each category. This process ensures that employees understand the importance of data security and know their responsibilities in protecting sensitive information.
A DLP policy serves as a framework for ensuring data security, maintaining compliance with regulations, and mitigating the risks associated with data breaches.
Here are the ten key reasons why your organization needs a DLP policy:
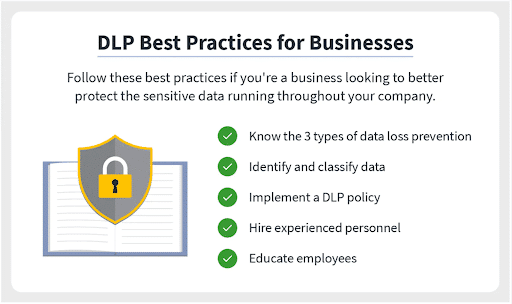
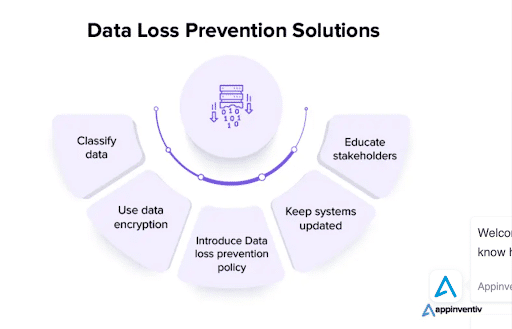
To build and implement a robust DLP policy, consider incorporating the following essentials or best practices:
By implementing these essentials and more into your DLP policy, you can establish a robust framework for data protection, reduce the risk of data loss incidents, and foster a security-conscious culture within your organization.
Learn more at: 12 Essentials for Every Data Loss Prevention Policy
Safeguarding organizational data has become more crucial than ever in the digital age, where the amount of data generated, stored, and shared is unprecedented. Remote work and digital communication’s rise has further intensified the need for Data Loss Prevention (DLP) policies.
To prevent the devastating consequences of data loss, organizations must prioritize their DLP policies and ensure they are comprehensive and effective. But effective data security can only be achieved when all employees are on board, and the organization has a security-forward culture.
CybeReady is an industry-leading cybersecurity awareness training platform that complements DLP efforts by focusing on employee training and awareness. Our AuditReady program ensures that your organization complies with regulations by training your teams and preparing you for unexpected audits. Our training programs are engaging, easy to deploy, and offer high-quality employee training.
Incorporating CybeReady’s training platform into your organization’s cybersecurity strategy can enhance your DLP efforts and prevent data loss incidents. With our compliance-driven training modules keeping your team aware, alert, and ready to identify and report threats, you can rest easier knowing your employees are equipped with the means to protect your organization’s data.
Schedule a demo to discover how to begin protecting your business data today with CybeReady’s training programs.





Copyright © 2025 – CybeReady
We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit
Wir werden uns in Kürze bei Ihnen melden.
Schauen Sie sich bitte in der Zwischenzeit das kostenlose CybeReady CISO Tool Kit an.
We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit, or visit Our Blog
We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit, or visit Our Blog