Get the latest & greatest cybersecurity insights straight to your inbox:



HOME > The Complete Guide to Smishing (SMS Phishing)
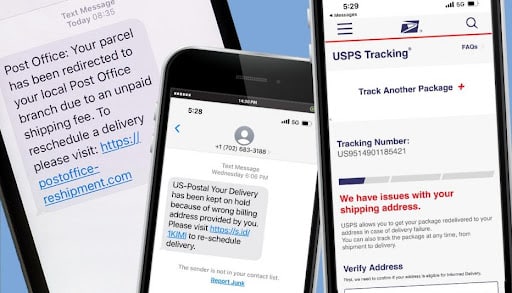
It’s unfortunately become an all-to-common scenario: you’re waiting for a package to be delivered—but then you receive an SMS text message that seems to be from the carrier, demanding payment before delivery can be completed. If you follow the link in the message, a look-alike website will be reached where you can enter your credit card information—and promptly have it stolen, along with your money. You’ve just become the latest victim of smishing.
Smishing is the name given to phishing scams run through SMS texting (the name being a portmanteau of SMS and phishing). This exact scenario played out for many Canadian customers awaiting package delivery from UPS during 2022 and 2023. Cybercriminals cracked an online package lookup tool and gained access to recipients’ data, including phone numbers, and began sending fraudulent SMS messages to the unaware victims.
One of the most recently prevalent forms of phishing attack, smishing exploded during the pandemic years and has become the bane of mobile phone owners everywhere. In this complete guide to smishing, we’ll dive deep into the murky waters of phishing and explain smishing in detail. We’ll identify smishing attacks, their risks and consequences, and learn how to prevent both phishing and smishing attacks.
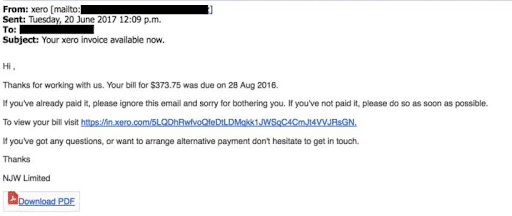
First, let’s briefly discuss phishing. A catch-all for a variety of deceptive cyber attacks, phishing manipulates individuals into divulging sensitive information or compromising their security. By mimicking trustworthy organizations or individuals, criminals earn the trust of unsuspecting victims and get them to click on malicious links or willingly provide personal or business information to a fake website or person.
The most common types of phishing are:
Attackers send emails, the most common phishing attack, posing as legitimate communications from well-known sources such as banks or government agencies. These emails often create a sense of urgency for recipients to provide personal information, click on malware-installing links, or download infected attachments.
This attack employs customized messages that appear even more legitimate because they include personal information about their intended victims. The UPS case discussed above might be described as “spear smishing.”
This attack specifically targets high-profile individuals such as CEOs or top-level executives. It employs impersonation tactics to trick them into revealing confidential business information or to get them to perform financial transactions.
In an attack that’s become easier due to voice-duplicating AI technology, phone calls are used to deceive individuals by impersonating reputable entities like banks or customer service representatives. The goal is to manipulate victims into revealing sensitive information over the phone.
Phishing attacks typically have a clear objective to obtain one or more of these four kinds of information:
Now that we understand the basics of phishing, we can discuss the latest version of phishing attacks—smishing.
Smishing, or SMS phishing, is a sneaky cyber attack that targets people through text messages on their mobile phones. It’s like phishing but specifically designed for mobile phones. The goal of smishing is to trick unsuspecting individuals into giving away their personal information or doing something that puts their security at risk.
Here’s how it works: hackers send text messages that look like they’re coming from trustworthy sources such as banks, government agencies, or popular brands (such as UPS in our previous example). These messages often contain urgent or tempting content that makes recipients feel they need to act immediately. The text messages might ask for sensitive details like passwords, credit card details, or Social Security Numbers. Or, they might include links that lead to malicious websites or downloads which infect devices with malware or steal personal data.
The sneaky part is that these text messages seem legitimate, and victims often trust them without question. After all, who wouldn’t believe a message from the post office saying there’s a problem with their parcel?
Smishing attacks typically have one or more of three objectives:
While smishing attacks leverage text messages and mobile devices due to their ubiquity and immediacy, phishing attacks primarily occur through email or fraudulent websites. But smishing and phishing share similar goals and strategies despite their different delivery methods.
Smishing and phishing attacks both:
Ultimately, both smishing and phishing attacks employ social engineering tactics to deceive and manipulate victims, with the goal of accessing sensitive information for malicious purposes.
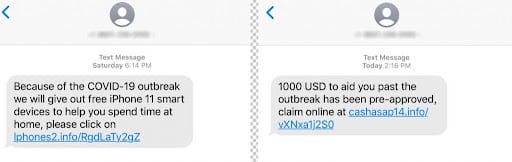
Smishing attacks have been on the rise, particularly throughout the pandemic, prompting official warnings from government authorities. As these attacks continue to escalate, it becomes essential for professionals across industries, particularly in finance, pharmaceuticals, and manufacturing, to be aware of the types, risks, and consequences of smishing.
Both individuals and organizations face significant risks from smishing attacks because these attacks exploit our trust in communication channels and try to trick us into divulging personal information or unwittingly installing malware. It is crucial for everyone to stay vigilant and take preventive measures to safeguard against the growing threat of smishing.
Smishing attacks take on various forms, each with distinct strategies and objectives. Here are some common types:
Attackers impersonate financial institutions, sending convincing messages to trick recipients into sharing sensitive banking details or login credentials.
Messages pretend to be from government agencies or law enforcement entities, sending seemingly official texts that demand immediate action or personal information.
These texts contain shortened URLs that, once clicked, lead to fraudulent websites that steal personal information or distribute malware.
Scammers send messages claiming the recipient has won a prize or lottery and ask for personal information or a fee to claim the supposed reward.
Exploiting people’s emotions, these messages create a sense of urgency, pressuring recipients to take immediate actions like making payments or revealing personal information.
Smishing attacks carry a range of risks with significant implications. It’s crucial to understand the following primary risks:
Understanding and addressing these risks is essential to safeguard personal and organizational security, protect sensitive data, and comply with relevant regulations.
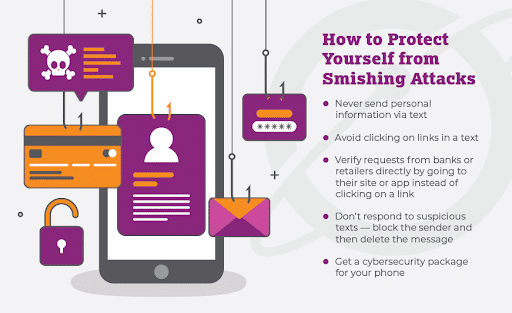
To protect yourself and your organization from smishing and phishing attacks, you can take several important steps. With the similarities we’ve noted between the two cyberattacks, you’ll find invaluable overlap in these preventative measures:
When receiving SMS messages or emails, exercising caution is crucial, especially when they request personal information or urge immediate action. It’s important to verify the sender’s identity before responding or clicking on any links.
Be wary of any unsolicited text messages, particularly those offering unexpected prizes, discounts, or urgent requests, because they could be smishing attacks to deceive you into sharing information or downloading harmful content.
Even if the sender appears familiar, remain skeptical of text messages that request personal information since legitimate organizations typically do not ask for sensitive information through text messages.
Activating 2FA on your personal and business online accounts is a critical measure to safeguard against smishing and phishing. Accessing your accounts requires a second verification step, usually a unique code sent to your mobile phone. Even if attackers managed to get your password, they would still need that additional code to gain entry. The extra step dramatically decreases the risk of unauthorized access, enhances the security of your accounts, and makes it significantly more challenging for them to be compromised.
Never share sensitive data via unsecured SMS text messages or email—and this applies to both personal and corporate data. Legitimate individuals or organizations will never ask you to provide this kind of information through either channel. Even if you have a secure email account, be sure to verify the sender before providing sensitive data.
Your mobile phone, personal computer, and work computer should all have up-to-date versions of robust anti-virus and anti-malware software. These will protect your device and its data in the event of malware or virus installation through a smishing or phishing attack. The best solutions also offer detecting, filtering, and reporting suspicious SMS and email messages.
One of the best ways to stop smishing and phishing cold in its tracks is through employee cybersecurity education and training that helps create a culture of awareness. A strong security culture can lower risks from cyber threats by motivating personnel to take security seriously, training them on best practices, and instilling a feeling of accountability for securing sensitive data.
The need to remain watchful and employ proactive measures to protect your business and yourself against cyber threats like smishing and phishing cannot be overstated. You can significantly strengthen your defenses against these attacks by being aware of the dangers involved, taking preventative action, and promoting a culture of cybersecurity awareness.
CybeReady provides training and educational solutions that strengthen the security posture of your business. To add an additional layer of cybersecurity to your defenses and keep one step ahead of the smishers and phishers.
Contact CybeReady today to discuss how our programs can help your organization stay safe.








Copyright © 2025 – CybeReady
Copyright © 2025 – CybeReady

We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit

We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit, or visit Our Blog

We will reach out to you shortly.
In the meantime, please check out our complimentary CISO Tool Kit, or visit Our Blog